When you automate processes with pdfToolbox, you mostly do so using profiles or process plans. A profile is a collection of checks and fixups, a process plan is a kind of “workflow” you can build in pdfToolbox using a visual flow editor that allows conditional processing, JavaScript and much more. If you have ever built such a profile or process plan, you might know that these profiles and process plans can contain many hours (even days) of configuration and testing work.
In pdfToolbox 14, a new possibility was built in; the ability to “protect” profiles or process plans. A protected profile can no longer be opened, so nobody can see how exactly you accomplished what you did. It can however be used by those people you give access.
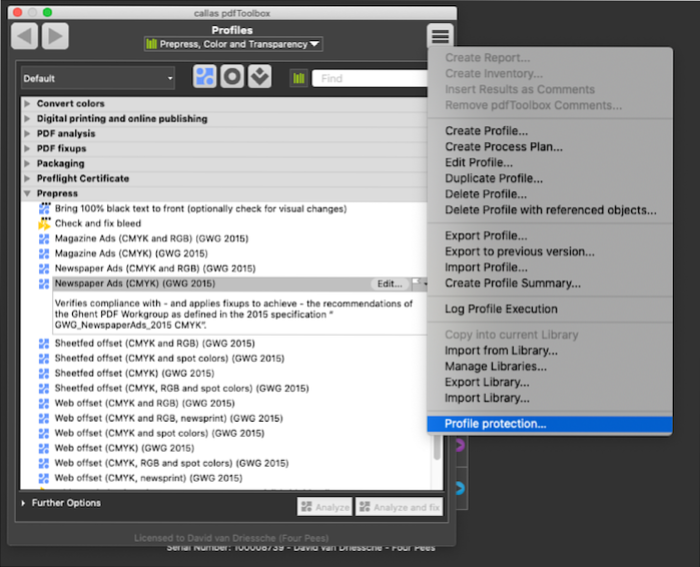
So, how to protect your profiles (or process plans)? Protecting profiles is easy. You open the profile protecting dialog window, and select all profiles and/or process plans you want to protect. Then, you can enter information for those protected profiles, including a name, description, version number and an information URL. Someone who is using the profiles can’t see what is inside the profile, but they can see this information instead. And then you select a password to protect the profiles with.
Who can use those profiles? This too is setup while you are protecting the profiles. Your first option is to allow everyone a trial period. This lets people import your profiles, and gives them access to use them (not inspect or edit them!) for the given number of days. The second option is to enter a list of pdfToolbox serial numbers; the pdfToolbox applications using those serial numbers then get total access to use the profiles (again, they can’t inspect or edit them!).
Share profiles. Once you protect your profiles, you can share them however you want and with whoever you want. If you granted a trial period, everyone receiving your profiles will be able to test them. And those serial numbers you granted permanent access, will be able to use them permanently.
Of course you can modify either the trial period, the serial numbers or both at any moment. Sold your library of profiles to another customer? Just add his serial numbers to the protected profiles, or save a set of profiles specifically for that customer and they can enjoy your pdfToolbox expertise!
Where is this feature supported? All of this works for all pdfToolbox flavors, including CLI and even if you are using it with a license server.
Protecting profiles is a smart new feature in pdfToolbox, especially for system integrators or resellers. Essentially, this allows them to create more complex profiles, protect them, and then sell them just as they would sell other services or software in the first place.
Resources: